In a press release, Crowdfense claims they're doing this to improve security.
Crowdfense today announces the launch of a $10 million (U.S.) bug bounty program to acquire and further develop active cyber-defense capabilities regarding some of the most popular software for Windows, MacOS, iOS and Android.However, in an interview with Motherboard, Crowdfense director Andrea Zapparoli Manzon reveals the startup intends to sell these exploits to law enforcement and intelligence agencies:
The company, which has spent more than a year in development, was designed by a global team of seasoned cyber-security experts, researchers and lawyers to work on some of the biggest cyber-defense challenges of our times and to introduce higher levels of professionalism and trust in this market.
"We work only with the best vulnerability researchers, focusing on very select capabilities with a highly structured and scientific approach," said Crowdfense director Andrea Zapparoli Manzoni. "Now that this originally underground practice has become a strategic high-tech industry, it is necessary to implement good business processes, checks and guarantees for all the parties involved. That is why we built Crowdfense: the market needed a neutral, reliable, law-abiding, process-driven partner to deliver top-quality active cyber-defense capabilities."
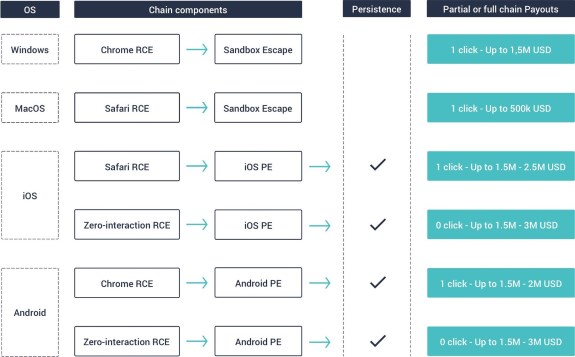
The first public bug bounty program by Crowdfense is offering payouts that have never been seen before.
The company is focused on quality over quantity, so that its institutional customers can get the best possible return on their investments, while successfully protecting their nations and citizens from a growing spectrum of threat actors.
“When I think about government agencies I don’t think about the military part, I think about the civilian part, that works against crime, terrorism, and stuff like that,” Zapparoli told me in a phone interview. “We only focus on tools aimed at doing activities of law enforcement or intelligence, not aimed at destroying or deteriorating the functionality and effectiveness of the target systems—but only aimed at collecting intelligence.”