Posted on Wednesday, October 30 2019 @ 11:12 CET by Thomas De Maesschalck
Speaking at the Open Source summit in Lyon, France, Linux kernel developer Greg Kroah-Hartman recommended the audience to disable Hyper-Threading on Intel CPUs if you want to be secure. For typical consumers this is not really an issue, but datacenters and enterprises will need to consider more carefully if they want to prioritize performance or security. Kroah-Hartman said this is the only way to fully protect yourself against MDS (Microarchitectural Data Sampling) CPU bugs as these flaws will remain with us for a long time. MDS vulnerabilities are easy to exploit, he said, and the hard part if that you can't tell if somebody is exploiting it.
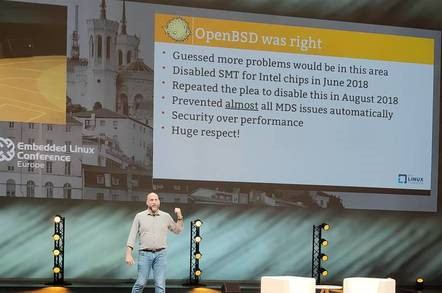
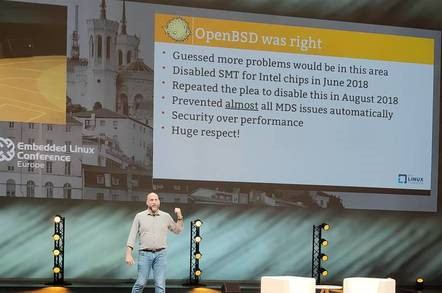
Open BSD was right, he said. "A year ago they said disable hyper-threading, there's going to be lots of problems here. They chose security over performance at an earlier stage than anyone else. Disable hyper-threading. That's the only way you can solve some of these issues. We are slowing down your workloads. Sorry."
Kroah-Hartman also dispelled the notion that Spectre is completely fixed, stating there have already been a couple of thousand patches for this issue alone:
Kroah-Hartman dispelled the idea that an issue like Spectre has a single fix. "We are still fixing Spectre 1.0 issues [almost] two years later. It's taken a couple of thousand patches over [almost] two years. Always take the latest kernel and always take the latest BIOS update."
He also mentioned that AMD CPUs seem safer, and that there's no evidence at this point about issues with AMD's implementation of SMT. Full details
at The Register.