Maxthon periodically uploads content to a webserver located in Beijing, China. The file is purported to be “image/pjpeg” but a closer look reveals it's actually an encrypted zip file with a dat.txt file.
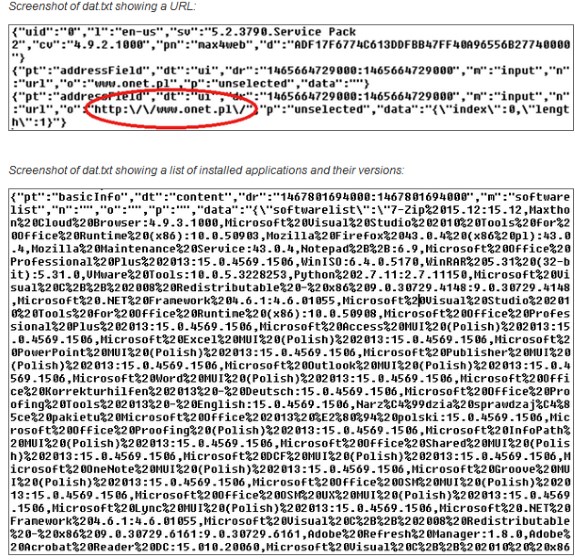
Once the security researchers figured out how to decrypt the dat.txt file, they discovered Maxthon phones home an astonishing amount of user data. This includes details about not only your PC configuration, but all websites you've visited, you're entire search history and a list of all installed programs including their version number:
OS version, screen resolution. CPU type/speed and amount of memory installed. Location of the Maxthon executable. Status of adblock (enabled or not, number of ads blocked). Homepage URL. Each and every full URL that the user visited (including the user’s google searches). List of installed applications including their version numbers.
Maxthon claims this behaviour is part of the company's User Experience Improvement Program’s (UEIP) to help with debugging and performance. A browser setting allows you to disable UEIP but Exatel and Fidelis observed data is being sent back to Maxthon regardless of the user's selection to participate in UEIP!
Not only is this level of surveillance worrying, Fidelis Cybersecurity also notes the data contains everything an attacker could need to craft a highly targeted attack. As such, Maxthon users would do well to remove the browser asap as it's essentially spyware. This is quite ironic as Maxthon markets itself as a browser with a tight focus on security and privacy, an image it banked on after the 2013 NSA surveillance scandal.