
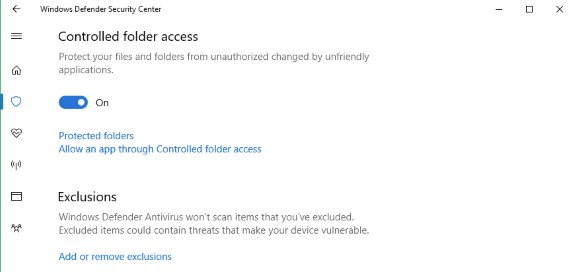
In this build, we’re making it easier for you to protect valuable data from malicious apps and threats, such as ransomware. To enable the feature, search for and open the Windows Defender Security Center from Start, go to the Virus & threat protection settings section, and set the switch to On:
Enable Controlled folder access.
Controlled folder access monitors the changes that apps make to files in certain protected folders. If an app attempts to make a change to these files, and the app is blacklisted by the feature, you’ll get a notification about the attempt. You can complement the protected folders with additional locations, and add the apps that you want to allow access to those folders.
Allowing apps can be useful if you’re finding a particular app that you know and trust is being blocked by the Controlled folder access feature. Click Allow an app through Controlled folder access and locate and add the app you want to allow.
Allowing apps can be useful if you’re finding a particular app that you know and trust is being blocked by the Controlled folder access feature.
You can add additional folders to the list of protected folders, but you cannot alter the default list, which includes folders such as Documents, Pictures, Movies, and Desktop. Adding other folders to Controlled folder access can be handy, for example, if you don’t store files in the default Windows libraries or you’ve changed the location of the libraries away from the defaults.
Click Protected folders in the Controlled folder access area and enter the full path of the folder you want to monitor. You can also enter network shares and mapped drives, but environment variables and wildcards are not supported (for right now).
Full details about the other new features in the Build 16232 can be found at the Windows Blog. There are also some Windows Defender Application Guard (WDAG) improvements plus exploit mitigation settings that can now be reached via the Windows Defender Security Center.
Presumably, these new features will be rolled out to the public in September/October with the Windows 10 Fall Update release.